Documentation Index
Fetch the complete documentation index at: https://docs.safefoundation.org/llms.txt
Use this file to discover all available pages before exploring further.
Overview
Safe Modules are smart contract extensions that add custom functionality to a Safe Smart Account. They operate alongside Safe’s core multi-signature logic and can execute transactions on behalf of a Safe according to their own rules. Modules allow Safe accounts to support automation, custom authorization schemes, and advanced workflows, while keeping this logic separate from the Safe core contracts. A basic Safe does not require any modules, but modules can be enabled or disabled through a Safe transaction approved by the required owner threshold. Multiple modules can be enabled at the same time, making Safe highly configurable for different use cases. Events are emitted whenever a module is added or removed, and when a module-initiated transaction succeeds or fails.Why use Safe Modules?
Safe Modules enable:-
Automation
Recurring payments, scheduled transactions, or automated DeFi interactions without manual approvals. -
Enhanced security controls
Rules such as spending limits, whitelists, or rate limits that restrict how funds can be used. -
Scalability
Complex logic can be delegated to specialized contracts instead of bloating the Safe core. -
Flexibility
Safes can be tailored to unique workflows, DAO operations, or integrations with DeFi protocols.
- daily or periodic spending allowances
- recurring payment and standing order modules
- social recovery modules that restore access if owners lose their keys
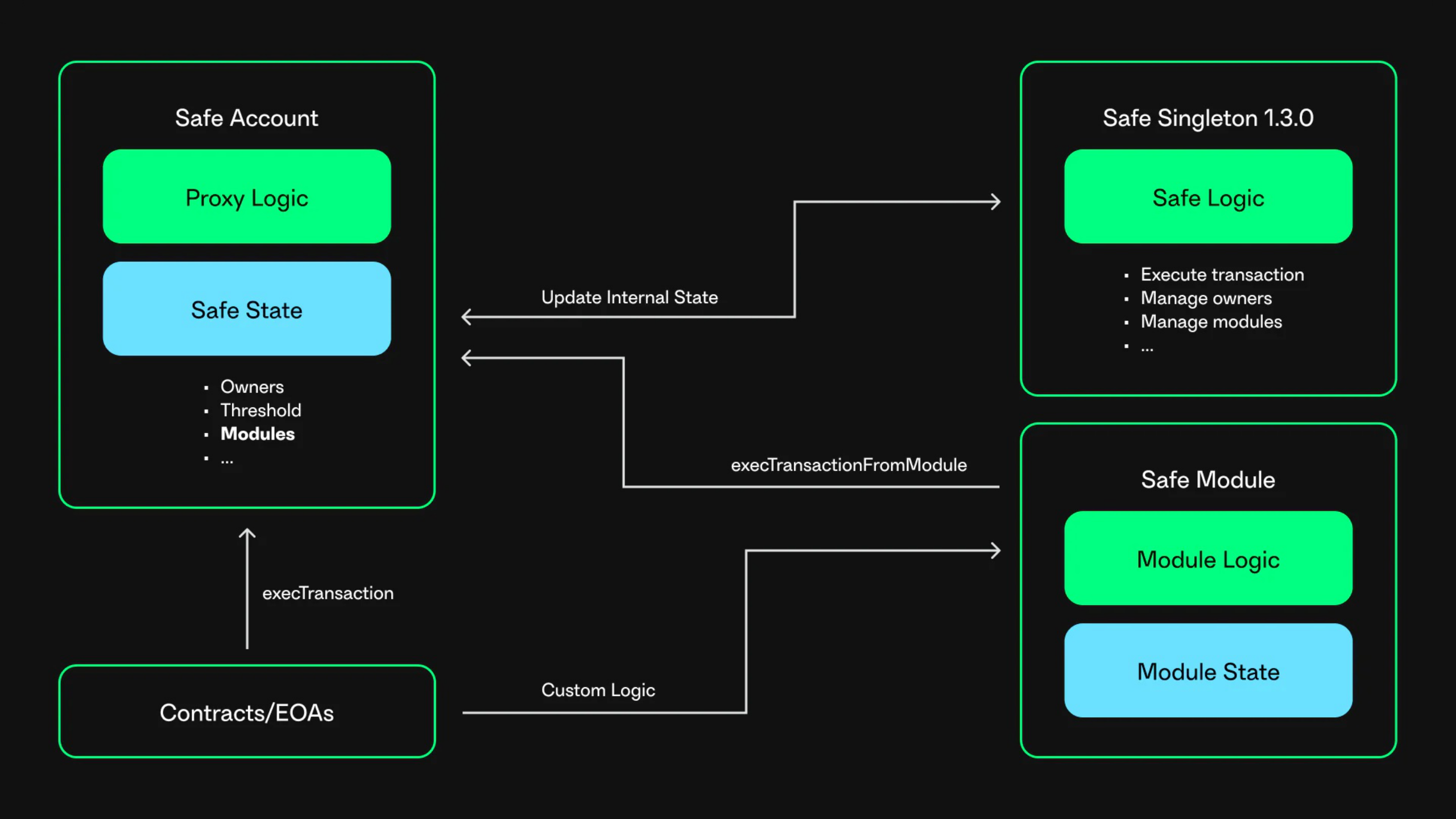
How Safe Modules work
-
Enable a module
A module is enabled by callingenableModule()through a Safe transaction.
The Safe stores the module address in an internal registry of authorized modules. -
Trigger a module action
A user (either an EOA or a contract) interacts with the module by calling one of its functions. -
Module validation
The module verifies that:- the caller is authorized
- the requested action complies with the module’s rules
-
Transaction execution
If the checks pass, the module callsexecTransactionFromModuleon the Safe to execute the transaction.
Creating a Safe Module
The best way to understand Safe Modules is to build one. A good starting point is the tutorial: Safe Modding 101: Create your own Safe ModuleExamples
Safe Modules are security-critical. Because modules can execute arbitrary
transactions on behalf of a Safe, only enable modules that are trusted,
well-reviewed, and audited. A malicious module can fully compromise a Safe.